
TECHNICAL SUPPORT & CONSULTING
In this computer dominated environment, hackers, malware, and viruses have crippled small to large networks...
95% of computers have been or will be affected by a virus or malware this year!
Don't be another statistic... We have you covered... Contact Us Today!

Computer Virus / Malware Removal & Prevention
We live in a world where just going to a site that have been comprimised can cripple an entire network or computerized device. Almost everything is connected to the internet. We rely the internet for banking, social media interaction, credit, and many other tasks.
In businesses, even one wrong site can lead to a company-wide disaster.
By keeping checks on systems and make sure they stay virus and malware clean, you can avoid alot of lost hours, sleep, & money cleaning up after the fact. Not to mention if a system is comprimised and collects banking, credit card info, or passwords for sensitive information etc. In fact, there are concerns for news sites that sell advertising space having malware coding lumped in with an ad that infects a computer system/network.
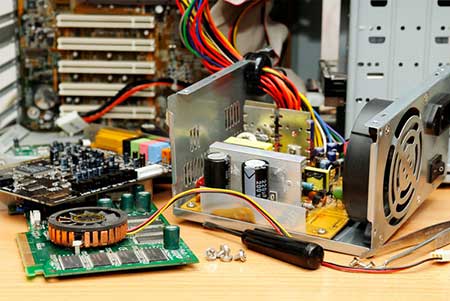
Computer Hardware Support / Networking
Not many things feel worse turning on a computer and getting a blue screen , sluggish performance, or not being able to access programs and data across a network due to hardware issues or failure.
By keeping your servers and computers maintained properly and regular diagnostics performed, most issues can be caught early before disaster strikes.
Or when something does inevitably fail, we can be there to help recover. With over 21 years experience in computer technology and computer networking, we have you covered!

Computer Monitoring / Security
Employee Monitoring
When too much personal time is being spent on business systems, or if people visit questionable sites on work systems, this can affect the bottom line of any business. You can keep recordings of computer activitiy and view activity graphs to determine where employees spend their time on a daily basis. This can also be vital in figuring out where a network threat or computing technology threat originated from to thwart future attacks.

Backup / Restore Solutions
"You shouldn't be doing any work at all in a computing environment without a reliable backup system and recovery strategy in place"
When (not if) a computing device or network server/device fails, there needs to be a recovery strategy in place.
Every piece of hardware has a life span. We usually don't know what that span will be. But when it fails, we need to be ready with a recovery plan and an on-site and off-site backup.
This is vital to any computing enviornment!

